Who knows what in sufficient time to make effective use of the news – that is as good a definition of ‘real-time’ intelligence, the gold standard of modern information practice, as is possible – was not often a military consideration in the classical world or even the age of Wellington. Alexander, Caesar, Wellington all operated within the peculiar constraint, to the modern way of thinking, of very slow communication speed over any distance not to be covered by a running man or a galloping horse. The best harkaras were credited with a speed of a hundred miles in twenty-four hours, but sceptics thought fifty more realistic. The modern marathon, whose runners achieve twenty-six miles in about three hours, gives a better indication of the nature of real-time intelligence before the coming of electricity. The armies, and navies, of the pre-electricity age operated within an intelligence horizon of considerably less than a hundred miles. Hence the enormous importance attached by the commanders of the past to strategic intelligence: the character of the enemy, the size and capability of his force, its dispositions, the nature of the terrain in his operational area and, more generally, the human and natural resources on which his military organisation depended. It was from guesses based on such factors that generals of the pre-modern world made their plans. ‘Real-time’ intelligence – where the enemy was yesterday, in which direction his columns were headed, where he might realistically be expected today – was arcane information, rarely to be collected on a real battlefield. As late as 1914, ten divisions of French cavalry, beating the Franco-German-Belgian border for nearly a fortnight, altogether failed to detect the advance of several million German troops. French reconnaissance forces failed again in the same area in 1940. Strategic intelligence is a desirable commodity. It rarely, however, brings advantage in actual time and space. For that, something else is necessary. What exactly is it? How is it possible to assure that the key questions, what, how, where and when, are answered to our advantage, not the enemy’s?
The acquisition of real-time intelligence requires, first of all, that the commander should have access to means of communication that considerably outstrip in speed that of the enemy’s movement over the ground, or water. Until the nineteenth century, the margin of superiority was very small. The marching speed of an army, reckoned at three miles per hour, was exceeded by that of a scout’s horse perhaps six times; but a scout had to make an outward as well as return journey, so the margin was halved. In the interval between scouts making contact with the enemy and returning, moreover, the enemy might advance, reducing the margin still further. Little wonder that surprise was so difficult to achieve in ancient campaigns. When it was, as spectacularly by the Seljuk Turks at Manzikert in 1071, the reason was often treachery or a total failure to reconnoitre, or both. At Manzikert the Byzantine army’s cavalry screen deserted, leaving the commander blind.
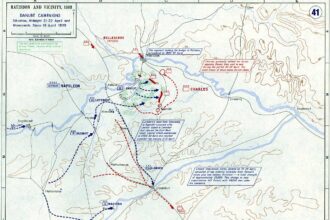
Manzikert was an ‘encounter’ battle, with both armies advancing simultaneously. More typical was the situation in which an advancing army ran into the outposts of an army standing on the defence. They automatically raised the alarm and, not having to go out and back, as in encounter operations, but back only, could give early warning. Wellington, for example, during the Waterloo campaign was, though strategically surprised, not so tactically. The French ran into his outposts, allowed him to fight a delaying battle at Quatre Bras on 16 June and to retire on to a previously reconnoitred main position at Waterloo two days later.
Surprise was equally as difficult to achieve at sea as it was on land until recent times. Indeed, the traditional problem in naval warfare was for opposing fleets to find each other at all. Hence the tendency for naval battles to occur in narrow waters, or ‘the shipping lanes’, often in areas where battles had occurred before. In theory, with the invention of the telegraphic flag code at the beginning of the nineteenth century, an admiral, by disposing his ships at the maximum limit of intervisibility – intervals of twelve miles – could, if his chain were long enough, create an early-warning screen which would cover several hundred miles of ocean. In practice admirals never had enough ships; and anyhow they preferred to keep those they had concentrated, for the danger of being brought to battle dispersed outweighed that of being surprised. An admiral surprised with his ships within range of recall could form line of battle; an admiral with his ships scattered on reconnaissance beyond quick recall had no such hope. Not until the invention of wireless telegraphy at the beginning of the twentieth century, and its adoption by war fleets, could admirals truly begin to command the far seas. Even then, old habits died hard. Sailors like to see.
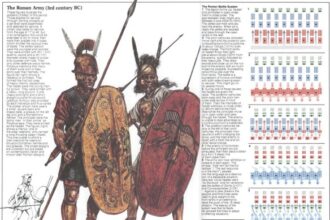
Sight is, of course, the principal and most immediate medium of real-time intelligence. It was so in the pre-telegraphic age and it has become so again in the age of electronic visual display. In the intervening period, which embraces the invention of the electric telegraph in the middle of the nineteenth century and its supersession by radio at the beginning of the twentieth, hearing acquired a superior status. It still enjoys something like parity. Radio in all its forms is an essential tool of military communication. Strategically it has become less important than the written message electronically communicated, by fax or e-mail. Tactically, it predominates, by immediacy and urgency. In the heat of engagement, voice-to-voice communication between commander and the front line, and in the opposite direction, is what makes battles work, a reality not altered since Caesar took personal, front-line control of the Tenth Legion against the Nervii on the River Sambre in 57 BC. ‘Calling to the centurions by name, and shouting encouragement to the rest’, Caesar transformed the tempo of the battle, shifting the psychological advantage to the Roman side and assuring the defeat of the Gauls.
The golden age of heard communication – the dot-dash of Morse telegraphy, the human voice of radio transmission – was comparatively short. It lasted in the military arena from about 1850 until the end of the twentieth century. It was a period punctuated by grave and frustrating blanks, particularly during the First World War, when the intensity of bombardment on the fixed fronts of west and east broke cable communication as soon as mobile operations began and the signal services had not yet succeeded in acquiring compact radios independent of cumbersome power supplies. Intelligence in real time became an impossibility. Commanders lost voice, indeed any other contact, with their forward troops over the shortest distances and battles degenerated into directionless turmoil.
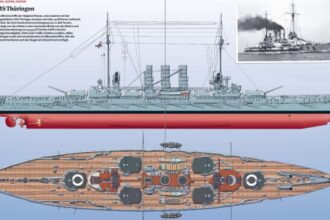
Not so at sea. Because of the ready availability of powerful electric current in turbine-propelled warships, radio communication within fleets and between their component units had become standard by 1914. There were difficulties; lack of directionality in contemporary transmitting sets made for interference, so intense in fleet actions that admirals continued to depend upon flag hoists to control their squadrons. Nevertheless, it had become clear by 1918 that the future of naval communications lay with radio.
Not, however, with radio telegraphy (R/T), as voice broadcasts were denoted to differentiate them from wireless telegraphy (W/T) in Morse code. R/T is insecure; the enemy overhearing it is as well informed as the intended recipient. Protection is possible, through very high-frequency (VHF) directional transmission, as in the Talk Between Ships (TBS) system used by anti-submarine escorts to great effect during the Battle of the Atlantic; but it is intrinsically short-range, as a secure means of speech. The only safe way of sending messages over long distances by radio wave is through encryption, effectively a return to W/T. Paradoxically, therefore, the flexibility and immediacy allowed by voice radio was denied, both strategically and, except in limited circumstances, tactically, by its insecurity. While the control of naval warfare became, as the twentieth century drew on, increasingly electronic, through the rise of such derivatives of radio as radar, sonar and high-frequency direction-finding (HF/DF), high-level, long-range communication remained stuck at the level of wireless telegraphy, because of the need to encrypt or encode, the resulting message being sent by Morse.
That imposed delay, which was why, though the same imperatives should have applied to army and air force communications, soldiers and airmen, caught up in the dynamics of close-range combat when time was too short to encrypt or encode, broadcast freely by voice radio. Tactical codes were developed – the British army’s Slidex, for example – but even Slidex took time. In the cockpit of a single-seat fighter, any form of encryption was impossible. All armies and air forces therefore set up tactical overhearing services, called ‘Y’ by the British, which listened in to the tactical voice radio transmissions of their opponents. Y frequently supplied battlefield intelligence of high value. During the Battle of Britain, for example, the British intercept stations were able to anticipate the warning of air raids supplied by the Home Chain radar stations by overhearing the chatter of Luftwaffe aircrew forming up before take-off on their French airfields.
Y was nevertheless of limited and local military value. Important radio communications were, from the First World War onwards, always encrypted or encoded and only a combatant equipped to render secret writing into plain text could hope to do battle on equal terms with the enemy. The competence of the major powers varied, between themselves and also over time. In the forty-five-year struggle between the Germans and the British during the twentieth century, for example, the Germans unknowingly lost the security of their naval codes early during the First World War and did not regain it. The British, partly by capture and partly by intellectual effort, were able to reconstruct their enemy’s book codes in 1914 and thereafter to read high-level German communications at will. In the aftermath of the war, hubris – a repetitive influence on secret communication – led the British to believe their own book codes impenetrable, while the Germans during the 1930s both broke the British book codes, an intrinsically insecure means of secret writing, and adopted a machine cipher system, Enigma, which would resist the attack of its enemies’ cryptanalysts – Polish, French and British – until well into the course of the Second World War. The Polish success in breaking Enigma before 1939 was negated before the outbreak of war by German variation of their machine encryption.
There are other means of acquiring intelligence in real time besides seeing and hearing, notably through the indirect sight provided by photographic intelligence and, today, satellite surveillance; human intelligence – humint, or spying – can, in certain circumstances, also convey critically urgent information. Both, however, are prone to delay and defect. Images, however acquired, need interpretation; they are often ambiguous and can cause experts to disagree. Thus, for example, photographic evidence brought back to Britain from the German pilotless weapons development station at Peenemünde during 1943 did show both the V-2 rocket and the V-1 flying bomb. The weapons went unrecognised for some time, however, in the first case because the interpretation officers did not recognise the rocket in its upright, launching position, in the second because the image of the V-1 was so small – less than two millimetres across – that it was missed. Yet the pilotless weapon photographic evidence was comparatively clear and was supported by other intelligence which told the interpreters what it was that they should be seeking to identify. They knew they were looking for ‘rockets’ and miniature aircraft; even so they failed to recognise the evidence before their own eyes. How much more difficult is image interpretation when the interpreters do not know exactly what the evidence will resemble when they see it: the hideouts of al-Qaeda terrorists, the bunkers of illegal Iraqi weapon development centres. The intelligence of imagery is frustratingly rich – many needles but in a vast haystack.
Human intelligence may suffer from different limitations, including, first, practical difficulty in communicating with base at effective speed and, second, inability to convince base of the importance of the information sent. The world of human intelligence is so wrapped about with myth that any clear judgement about its usefulness is difficult to establish. It does seem, however, that, for example, the Israeli foreign intelligence service was running an ‘agent in place’ at a high level in Egypt before that country’s attack on Israel in 1973. Because the Egyptian government dithered over the decision to attack, the agent sent a succession of self-cancelling reports, with the result that, when the attack came, the Israeli army had gone off high alert. True or not, the story leaves unresolved the question of how the agent was able to communicate in real time. The case of Richard Sorge was entirely different; he was both highly placed and well equipped to communicate, by clandestine radio. His difficulty – of which he was unaware – was to secure a hearing. Sorge, a committed Communist and long-term Comintern agent, had established himself before the Second World War in Tokyo as the respected correspondent of a German newspaper. As a German native and citizen, thought to be entirely patriotic, he became intimate with the staff of the German embassy, passed on information about Japanese affairs the diplomats found useful and eventually began to assist the ambassador in drafting his reports to Berlin. As a result, he was able to send the assurance to Moscow, during the terrible summer of 1941, that Japan did not intend to assist its German ally by attacking the Soviet Union through Siberia. He had earlier sent convincing warning of Germany’s intention to invade and had even identified the correct date, 22 June. Stalin had received other warnings, including one from Churchill, but chose to ignore them, as he ignored that of Sorge. The idea of war was too uncomfortable; Stalin preferred to believe that he could buy Germany off, by fulfilling delivery of strategic materials, including oil. As to the assurance that Japan would not invade Siberia, the evidence is that Stalin had moved a large portion of the Soviet garrison out of Siberia before the attack of 22 June and that Sorge’s warning, even if heeded, was not the critical strategic intelligence it seemed to be.
Other celebrated human intelligence organisations of the Second World War, the ‘Red Orchestra’ in Germany and the ‘Lucy Ring’ in Switzerland, also lack credibility as media of real-time intelligence, though for different reasons. Sorge is almost unique among identified operators in the world of humint by reason of his undoubted access to information of high quality and his ability to forward it speedily to base. The Red Orchestra, a coterie of left-inclined Germans of superior social standing, was a dilettante organisation, led by a Luftwaffe officer with a double-barrelled name, who seem to have been animated by the excitement of misbehaviour. They transmitted little of importance to Moscow, betrayed themselves by lack of elementary security precautions and were rapidly rolled up the Gestapo. The information supplied by the Lucy Ring – in reality an individual called Rudolf Roessler – to Moscow from Switzerland during the war seems largely to have been derived from his study of the German press. The rest was fed to him by the Swiss, who maintained contacts with the German Abwehr. The Swiss feared that a German victory would lead to the incorporation of their country into a greater Reich; the Abwehr was adept at playing a double, if impenetrable game. Roessler may have belonged to that colourful gang of fantasists who enriched themselves, at the expense of the secret service budgets of many countries, throughout the Second World War. In any case, he lacked a radio link to Moscow.
The ability to communicate, quickly and securely, is at the heart of real-time intelligence practice. It is rarely enjoyed by the agent, that man of mystery who figures so centrally in the fictional literature of espionage. Real agents are at their most vulnerable when they attempt – by dead letter box, microdot insertions in seemingly innocent correspondence, meetings with couriers, most of all by radio transmitter – to reach their spymasters. The biographies of real agents are ultimately almost always a story of betrayal by communication failure. A high proportion of the Special Operation Executive (SOE) agents in France during the Second World War were discovered by German radio counter-intelligence; the same was true of those operating in Belgium while, as has become well known, at one stage all agents dropped into Holland were collected on site by German manipulators of the SOE radio network. Even when counter-intelligence is deplorably lax, as in the notorious ‘Missing Diplomats’ case, the certainty of Donald Maclean’s guilt was finally established, even if retrospectively, by his habit of leaving Washington to meet his Soviet controller in New York twice a week.
It is the intrinsic difficulty of communication, even, indeed above all, for the agent with ‘access’, which limits his – or occasionally her – usefulness in real time. By contrast, the enemy’s own encrypted communications, if they can quickly be broken, will, of their nature, provide intelligence of high quality in real time.
The history of ‘how, what, where, when’ in military intelligence is therefore largely one of signal intelligence. Not exclusively; human intelligence has played its part and so, latterly, has photographic and surveillance intelligence. In principle, however, it is the unsuspected overhearings of the enemy’s own signals which have revealed his intentions and capabilities to his opponent and so allowed counter-measures to be taken in time.
It has become part of the conventional wisdom that intelligence is the necessary key to success in military operations. A wise opinion would be that intelligence, while generally necessary, is not a sufficient means to victory. Decision in war is always the result of a fight and in combat willpower always counts for more than foreknowledge. Let those who disagree show otherwise.
Chief:
Now remember, now that we know that KAOS is in possession of the stolen plans, what we have to find out is how they intend to smuggle them out of the country and when.
Maxwell Smart:
Yes. Well, what you’re saying, Chief is that now that we know how, all we have to do is find out who, when and where.
Chief:
No, forget about where. When we find out how, we’ll know where.
Maxwell Smart:
Well, how will how tell us where?
Chief:
If it’s going by boat, it’s probably going to Richelieu’s salon in Beirut, which is a safe port. If it’s going by plane, it’ll probably go to his salon in Damascus. You understand?
Maxwell Smart:
Yes, I understand Chief, but I don’t think I quite agree with you. You see all you’ve told me is that we know how but we don’t know who, when or where. So that tells us that we don’t know anything.
Chief:
[blinks] What?
Maxwell Smart:
Well, we know who, and that doesn’t tell us when, so why should how tell us where?
Chief:
Max, you’re driving me crazy.
Maxwell Smart:
How?
Chief:
Don’t say that word!
Maxwell Smart:
Why?